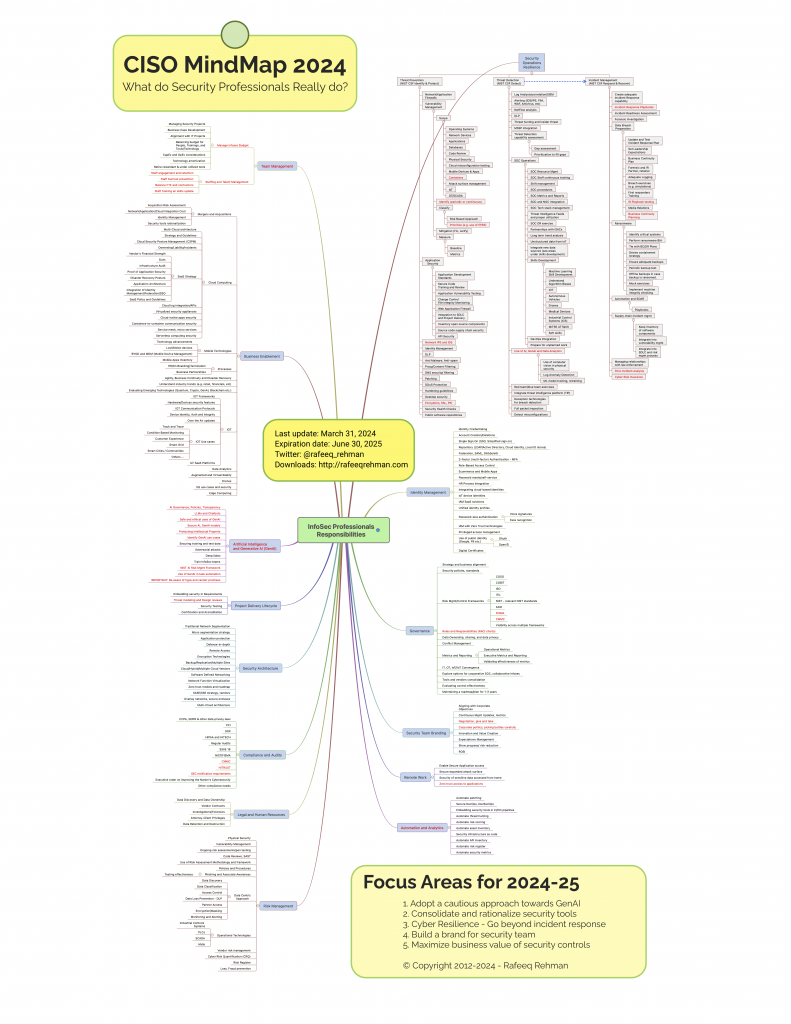
CISO MindMap 2024: What do InfoSec Professionals Really Do?Rafeeq Rehman | Cyber Security | Board Advisory
Many individuals outside the realm of cybersecurity often underestimate the intricacies involved in a security professional’s role. Since its inception in 2012, the CISO MindMap has served as a valuable educational resource, offering insights into CISO responsibilities and aiding security … Continue reading →| Rafeeq Rehman | Cyber Security | Board Advisory