How works Microsoft Defender Vulnerability Management (MDVM)
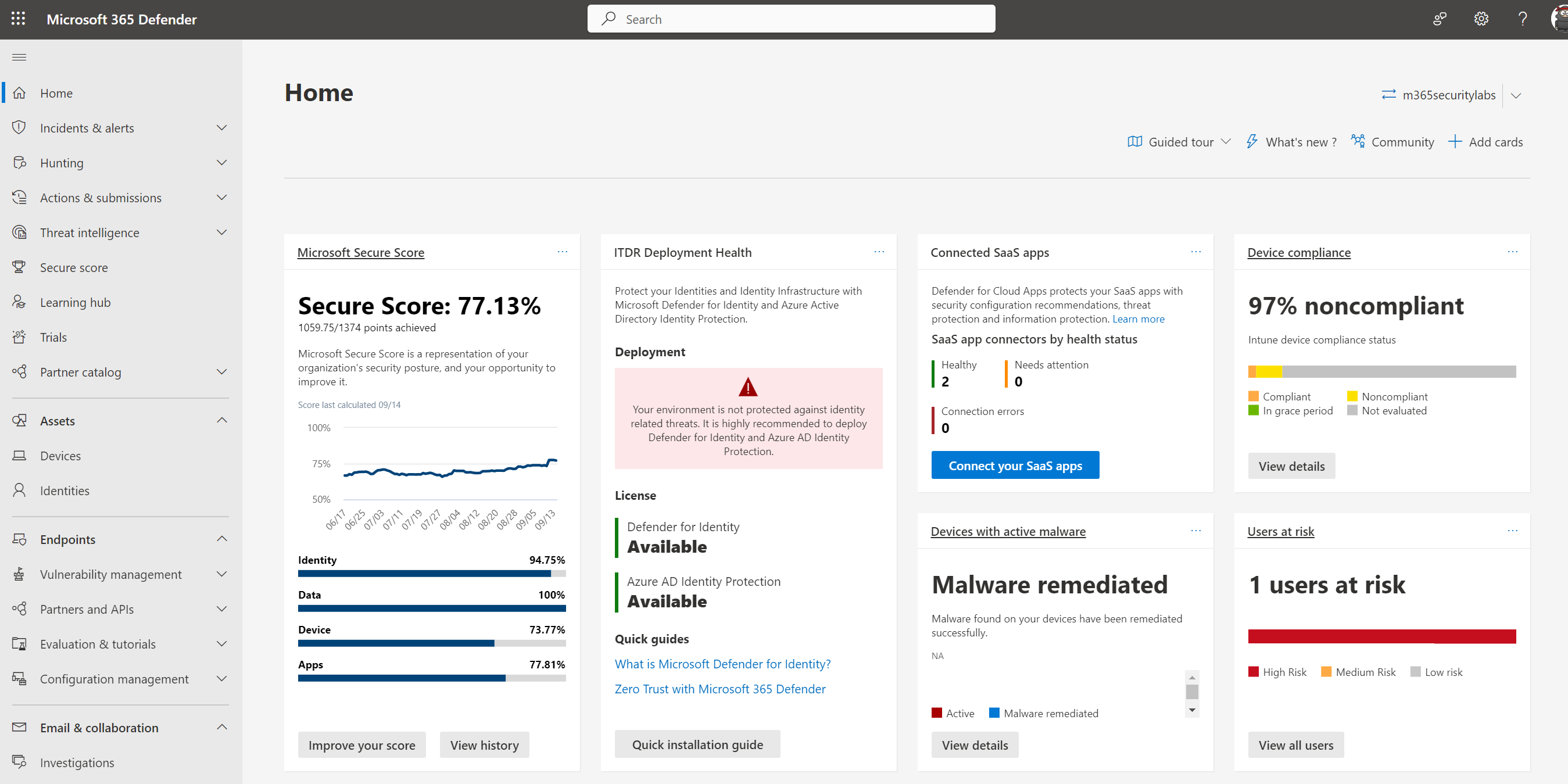
It is time for part 5 of the Microsoft Defender for Endpoint (MDE) series. All previous parts were focused on the Defender for Endpoint onboarding and configuration. Now it is time for the initial usage of the Defender for Endpoint...| Jeffrey Appel - Microsoft Security blog